What is Cybersecurity?
Cybersecurity is deploying proper measures to be protected from criminal and unauthorized use of your company’s data. Cyber attacks can attack either the confidentiality, the availability, or the integrity of your data, and it is critical to secure yourself from all kinds of attacks.
Common Risks From Cyber Attack
How Can your Business Be Hurt by a Data Breach
- The average data breach can cost a company over $3.5 million
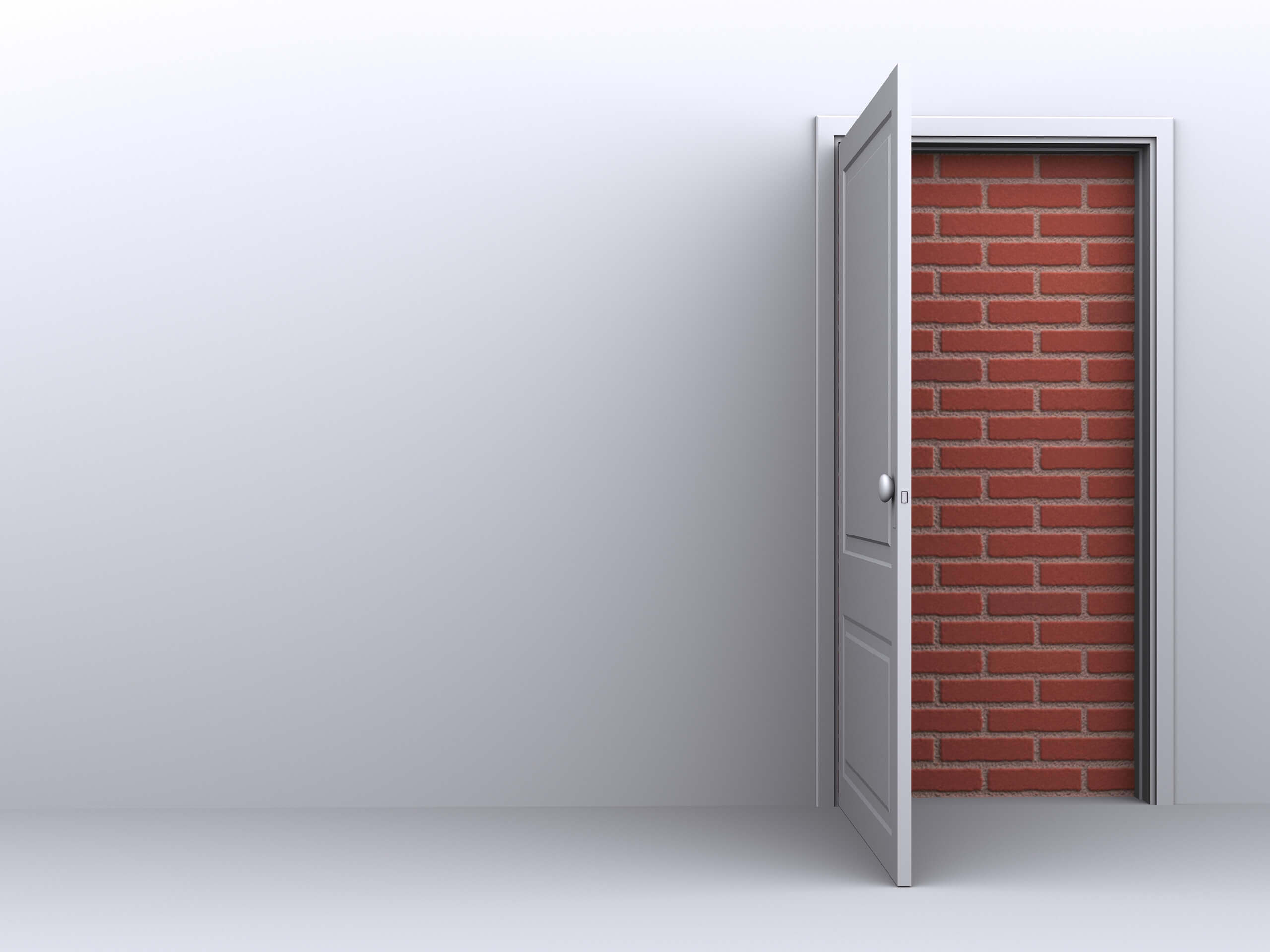
- Over 60% of SMBs are forced to close their doors within six months of a cyber attack
- Damages from data breaches extend beyond dollars and cents and hit company’s in what matters most trust and reputation